Indicators of compromise
editIndicators of compromise
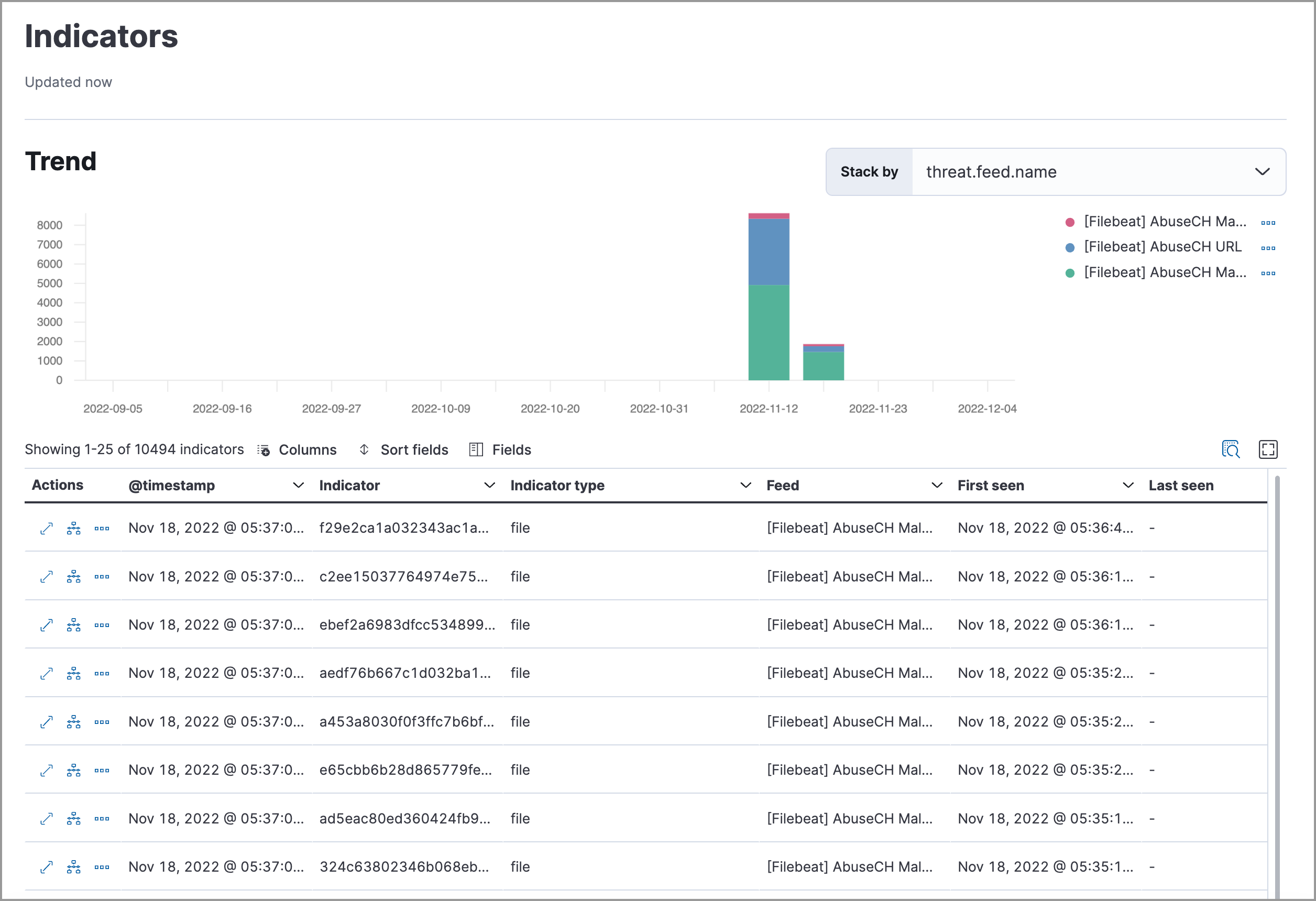
editThe Indicators page (Intelligence → Indicators) collects data from enabled threat intelligence feeds and provides a centralized view of indicators, also known as indicators of compromise (IoCs). This topic helps you set up the Indicators page and explains how to work with IoCs.
Threat intelligence and indicators
editThreat intelligence is a research function that analyzes current and emerging threats and recommends appropriate actions to strengthen a company’s security posture. Threat intelligence requires proactivity to be useful, such as gathering, analyzing, and investigating various threat and vulnerability data sources.
An indicator, also referred to as an IoC, is a piece of information associated with a known threat or reported vulnerability. There are many types of indicators, including URLs, files, domains, email addresses, and more. Within SOC teams, threat intelligence analysts use indicators to detect, assess, and respond to threats.
Set up the Indicators page
editInstall a threat intelligence integration to add indicators to the Indicators page.
-
Choose one of the following:
- From the Elastic Security app main menu, go to Intelligence → Indicators → Add Integrations.
-
From the Kibana main menu, click Add integrations. In the search bar, search for
Threat Intelligenceto get a list of threat intelligence integrations.
-
Select a threat intelligence integration, then complete the integration’s guided installation.
For more information about available fields, go to the Elastic integration documentation and search for a specific threat intelligence integration.
- Return to the Indicators page in Elastic Security. Refresh the page if indicator data isn’t displaying.
Troubleshooting
editIf indicator data is not appearing in the Indicators table after you installed a threat intelligence integration:
-
Verify that the index storing indicator documents is included in the default Elastic Security indices (
securitySolution:defaultIndex). The index storing indicator documents will differ based on the way you’re collecting indicator data:-
Elastic Agent integrations -
logs_ti* -
Filebeat integrations -
filebeat-*
-
Elastic Agent integrations -
- Ensure the indicator data you’re ingesting is mapped to Elastic Common Schema (ECS).
Indicators page UI
editAfter you add indicators to the Indicators page, you can examine, search, filter, and take action on indicator data. Indicators also appear in the Trend view, which shows the total values in the legend.
Examine indicator details
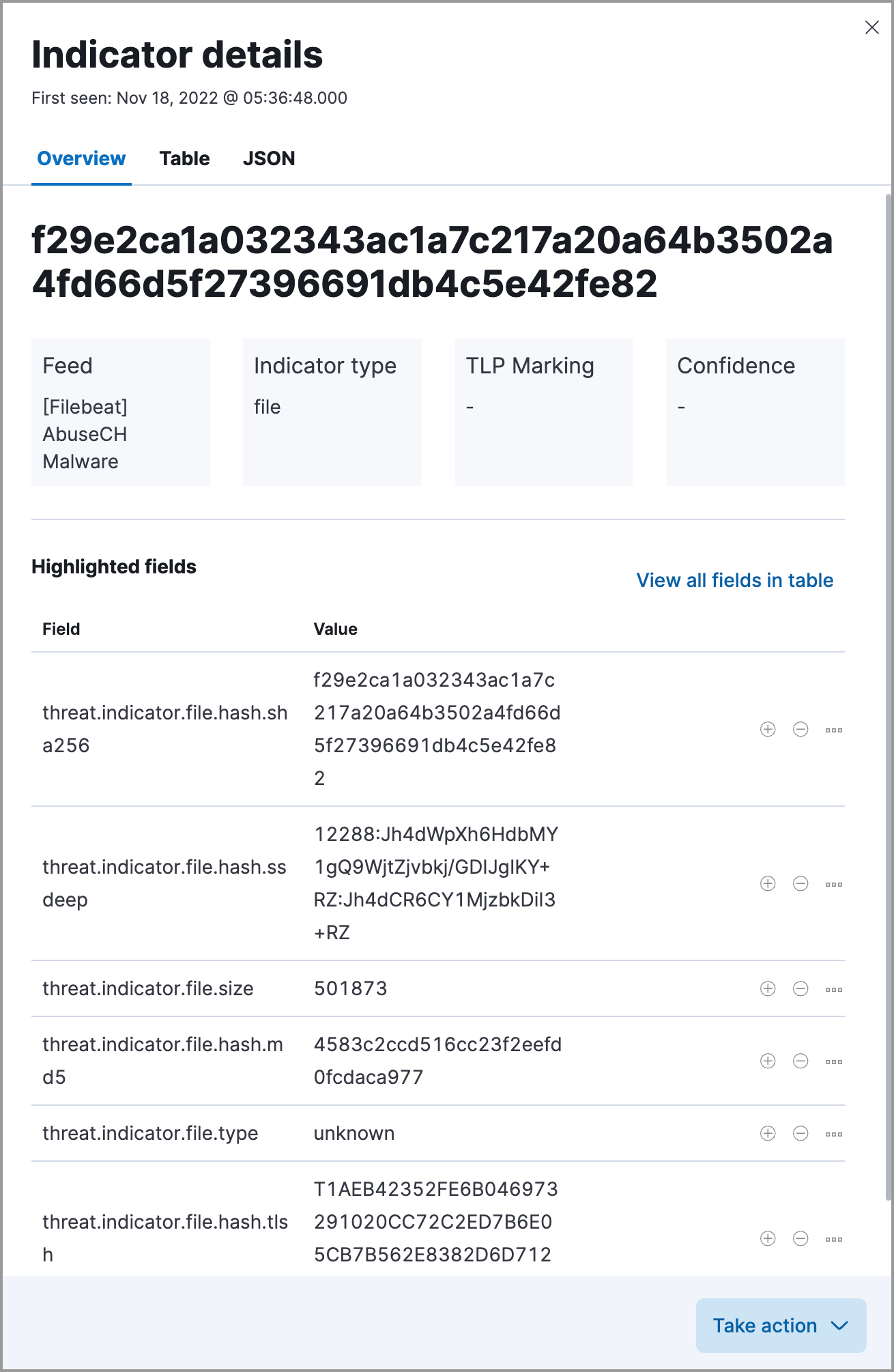
editLearn more about an indicator by clicking View details, then opening the Indicator details flyout. The flyout contains these informational tabs:
-
Overview: A summary of the indicator, including the indicator’s name, the threat intelligence feed it came from, the indicator type, and additional relevant data.
Some threat intelligence feeds provide Traffic Light Protocol (TLP) markings. The
TLP MarkingandConfidencefields will be empty if the feed doesn’t provide that data. - Table: The indicator data in table format.
-
JSON: The indicator data in JSON format.
Find related security events
editInvestigate an indicator in Timeline to identify and predict related events in your environment. You can add an indicator to Timeline from the Indicators table or the Indicator details flyout.
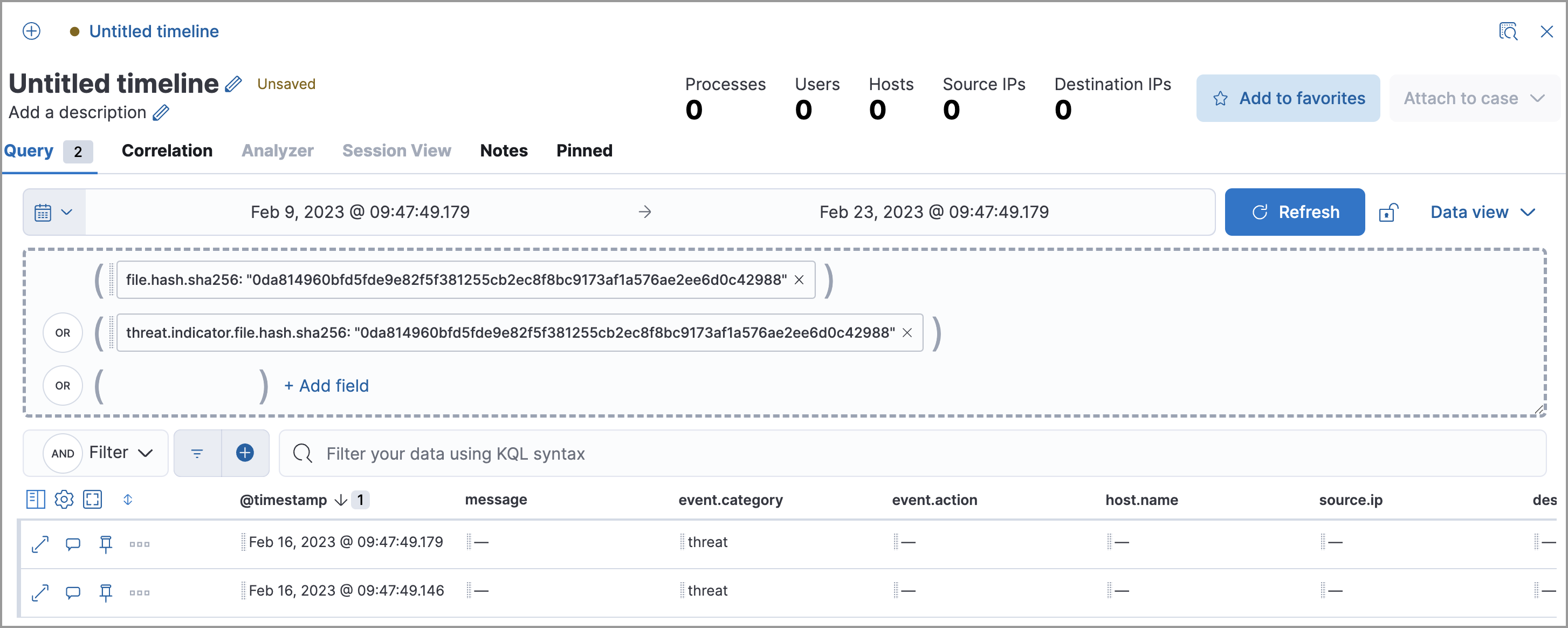
When you add an indicator to Timeline, a new Timeline opens with an auto-generated KQL query. The query contains the indicator field-value pair that you selected plus the field-value pair of the automatically mapped source event. By default, the query’s time range is set to seven days before and after the indicator’s timestamp.
Example indicator Timeline investigation
editThe following image shows a file hash indictor being investigated in Timeline. The indicator field-value pair is:
threat.indicator.file.hash.sha256 : c207213257a63589b1e1bd2f459b47becd000c1af8ea7983dd9541aff145c3ba
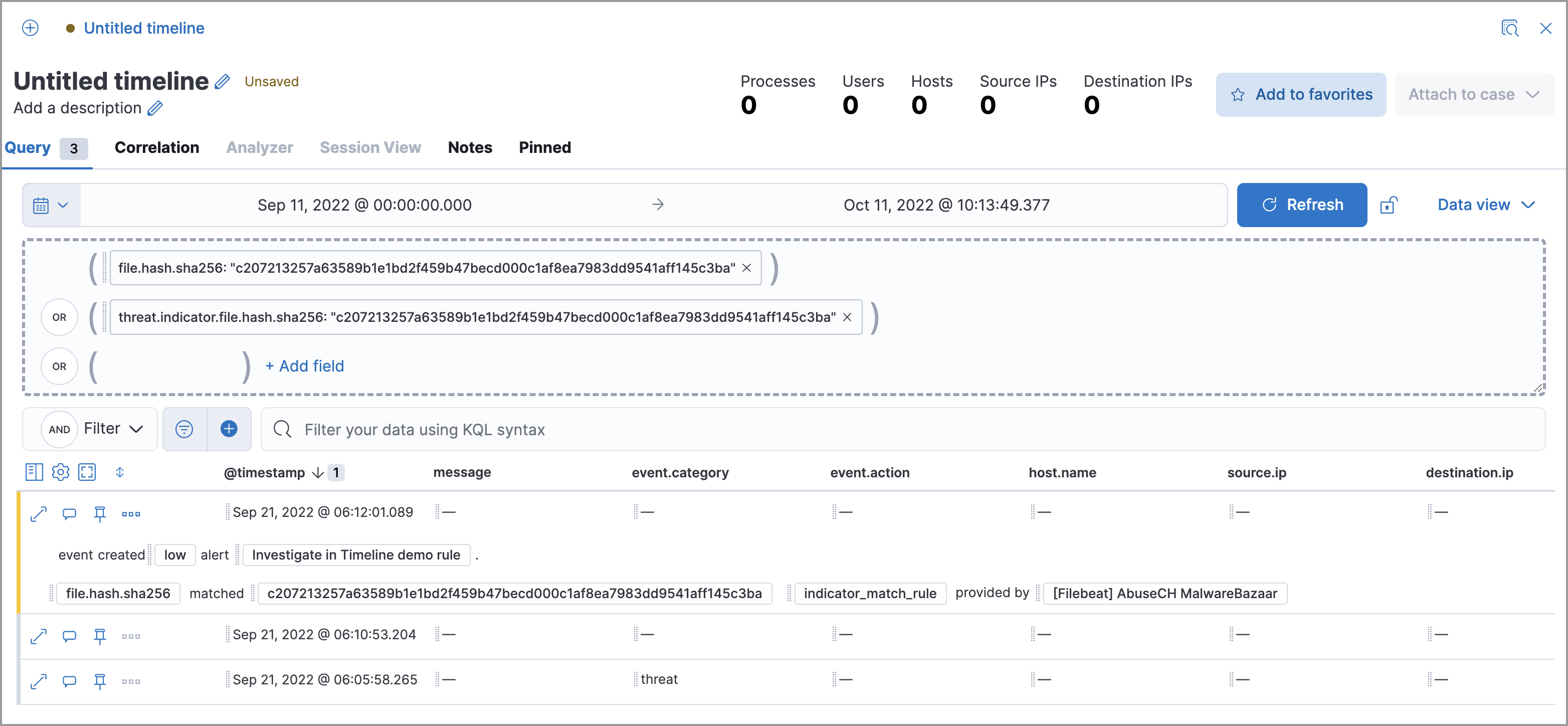
The auto-generated query contains the indicator field-value pair (mentioned previously) and the auto-mapped source event field-value pair, which is:
file.hash.sha256 : c207213257a63589b1e1bd2f459b47becd000c1af8ea7983dd9541aff145c3ba
The query results show an alert with a matching file.hash.sha256 field value, which may indicate suspicious or malicious activity in the environment.
Attach indicators to cases
editAttaching indicators to cases provides more context and available actions for your investigations. This feature allows you to easily share or escalate threat intelligence to other teams.
To add indicators to cases:
- From the Indicators table, click the More actions (…) menu. Alternatively, open an indicator’s details, then select Take action.
-
Select one of the following:
- Add to existing case: From the Select case dialog box, select the case to which you want to attach the indicator.
- Add to new case: Configure the case details. Refer to Open a new case to learn more about opening a new case.
The indicator is added to the case as a new comment.
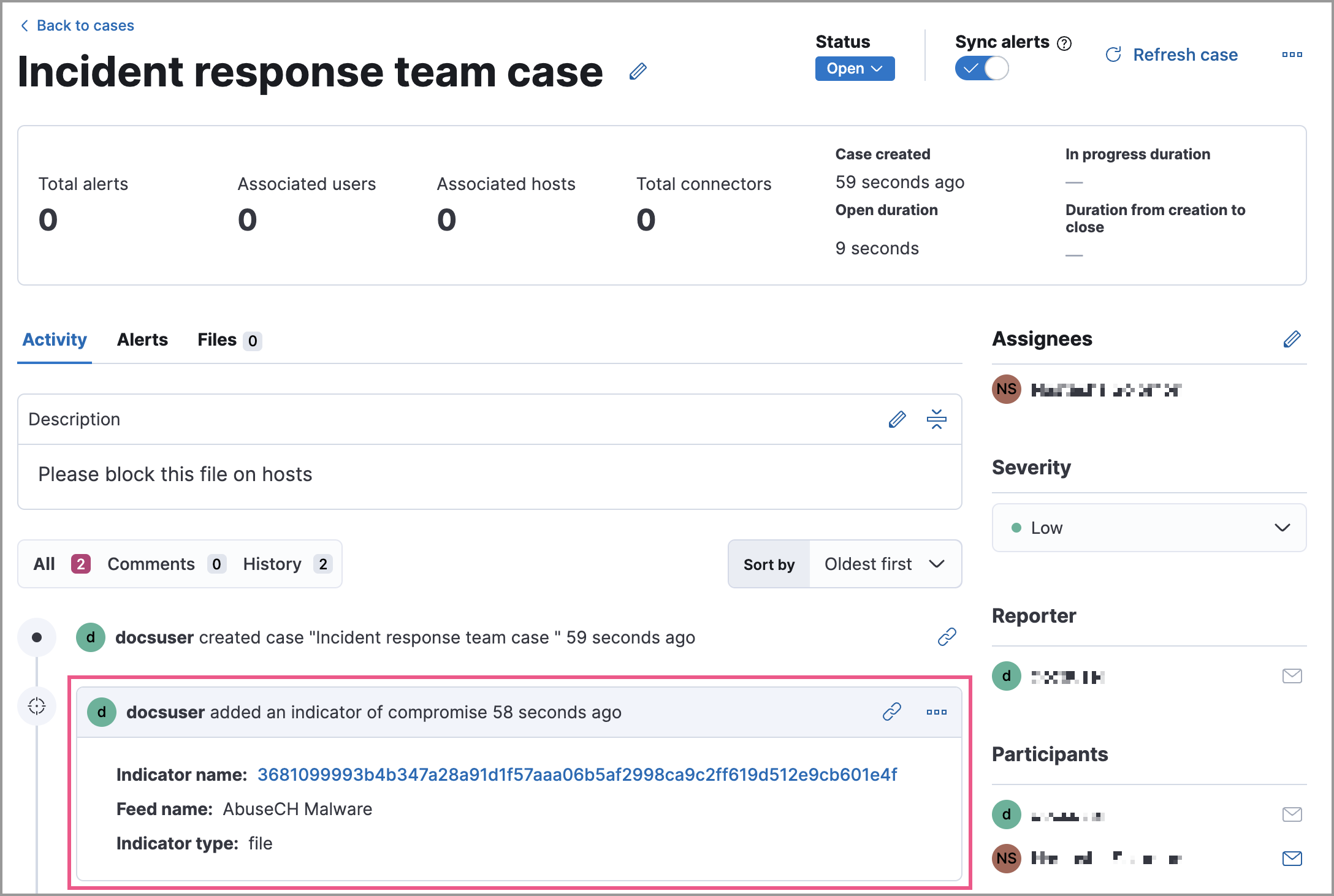
Review indicator details in cases
editWhen you attach an indicator to a case, the indicator is added as a new comment with the following details:
-
Indicator name: Click the linked name to open the Indicator details flyout, which contains the following tabs:
-
Overview: A summary of the threat indicator, including its name and type, which threat intelligence feed it came from, and additional relevant data.
Some threat intelligence feeds provide Traffic Light Protocol (TLP) markings. The
TLP MarkingandConfidencefields will be empty if the feed doesn’t provide that data. - Table: The indicator data in table format.
- JSON: The indicator data in JSON format.
-
- Feed name: The threat feed from which the indicator was ingested.
-
Indicator type: The indicator type, for example,
fileor.exe.
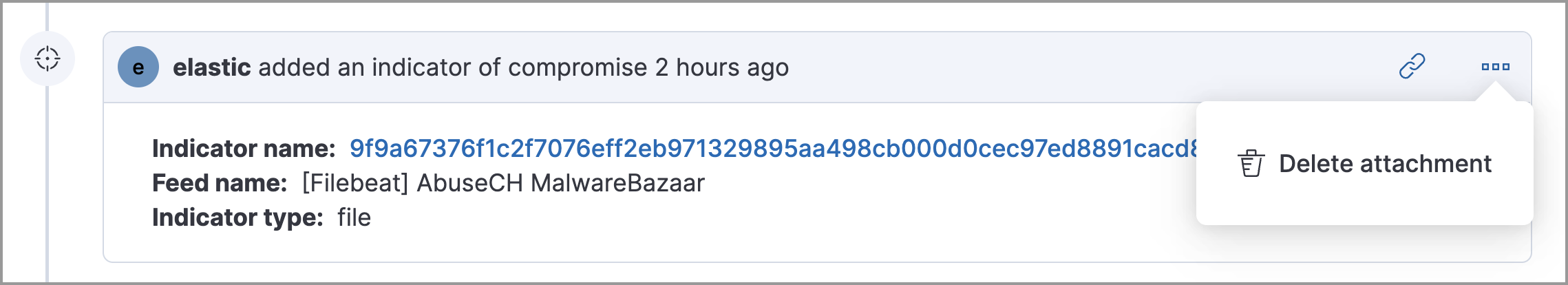
Remove indicators from cases
editTo remove an indicator attached to a case, click the More actions (…) menu → Delete attachment in the case comment.
Use data from indicators to expand the blocklist
editAdd indicator values to the blocklist to prevent selected applications from running on your hosts. You can use MD5, SHA-1, or SHA-256 hash values from file type indicators.
You can add indicator values to the blocklist from the Indicators table or the Indicator details flyout. From the Indicators table, select the More actions (…) menu → Add blocklist entry. Alternatively, open an indicator’s details, then select the Take action menu → Add blocklist entry.
Refer to Blocklist for more information about blocklist entries.